We are pleased to announce Synex Server 13 R4, an update that expands ServerHub's capabilities toward centralized identity and authentication management. The main component of this version is the FreeIPA module, the first addition to the new "Identity & Access Management" category that complements the existing ecosystem of enterprise modules.
FreeIPA: centralized authentication and enterprise directory
FreeIPA is an integrated identity management solution developed by Red Hat that combines LDAP, Kerberos, DNS, and certification services in a unified platform. The ServerHub module provides automated deployment of FreeIPA Server through Docker container, eliminating the installation and configuration complexity that traditionally requires this type of infrastructure.
What FreeIPA provides
Centralized authentication: Single Sign-On (SSO) through Kerberos for the entire infrastructure. Users authenticate once and gain access to all configured services without re-entering credentials.
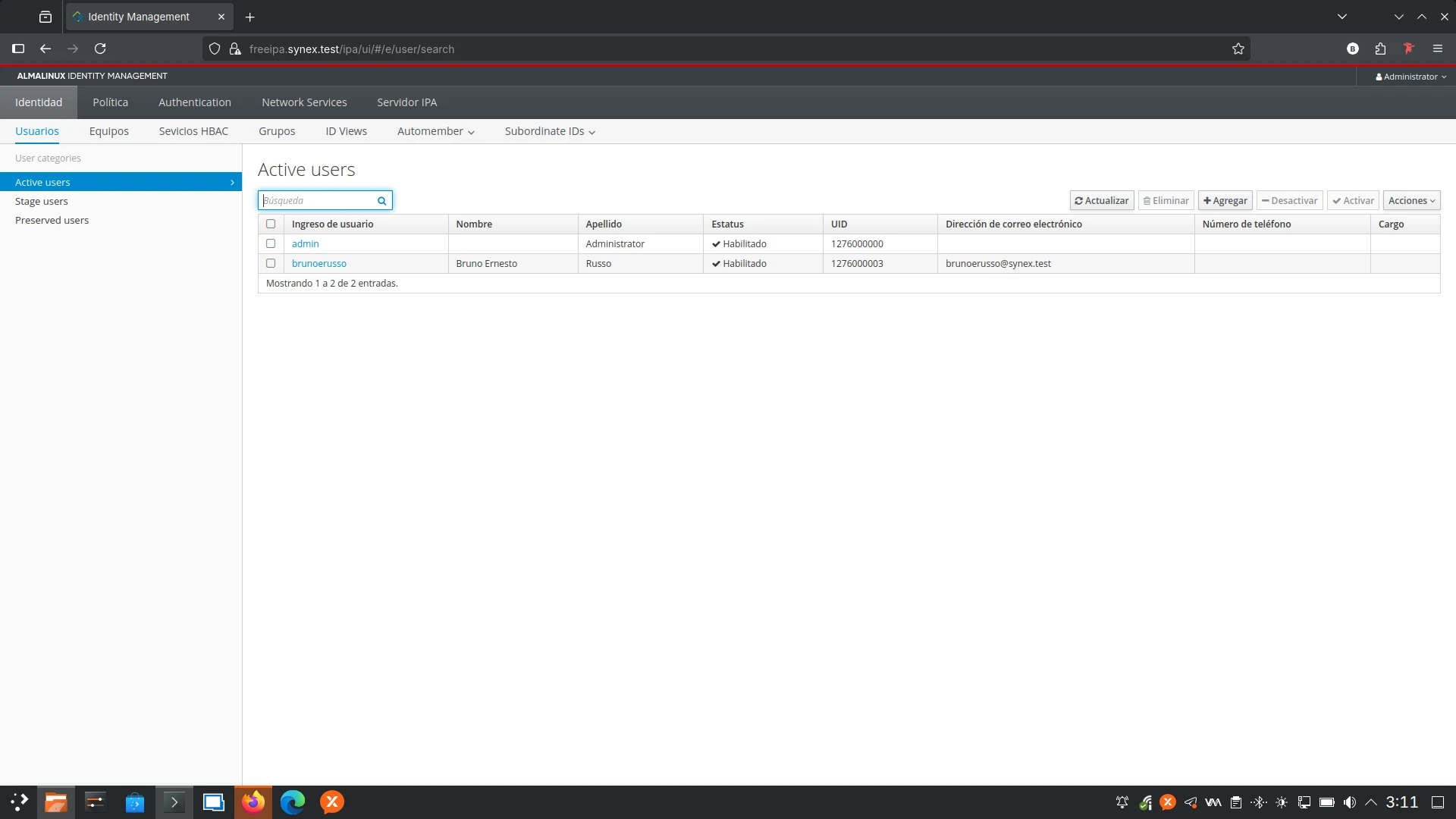
LDAP directory: Centralized database of users, groups, hosts, and services. All identity information resides in a single manageable point through web interface or command line.
Integrated DNS: Authoritative DNS server with complete support for SRV records required by Kerberos and LDAP. Name resolution is an integral part of the authentication system, not an external component.
Certificate authority: Internal PKI that issues and manages SSL/TLS certificates for services and users. Certificates are integrated with LDAP identities and can be used for certificate-based authentication.
Host-based access control (HBAC): Granular policies that define which users can access which hosts, from which locations, and through which services. Access control is part of the directory, not scattered local configurations.
Implementation in ServerHub
The module implements FreeIPA Server using the official freeipa/freeipa-server:almalinux-10 image through Docker Compose. The container architecture requires specific configurations that the module manages automatically: cgroup mode host for systemd control, /sys/fs/cgroup mounting, tmpfs for /run and /tmp, and mapping of all ports required by integrated services.
The installation automatically detects the server's IP address and network gateway, configuring FreeIPA with these parameters without user intervention. The initial domain uses .test (reserved by IANA for test environments according to RFC 6761) avoiding conflicts with mDNS/Avahi that affect .local. Administrators can reconfigure the domain later from the FreeIPA web console when migrating to production.
Credentials and security
The module generates a random 24-character password for the FreeIPA administrative account during installation. Credentials are stored in /root/.freeipa_credentials with 600 permissions, ensuring that only root can access this critical information. The file contains:
- Administrative user (admin)
- Generated password
- Kerberos realm
- Base domain
- Web interface access URL
This approach balances security (complex random password) with accessibility (credentials documented in a known location for the system administrator).
Installation process and startup time
The initial FreeIPA deployment requires several minutes. The container executes ipa-server-install -U with automatically detected parameters, a process that includes:
- LDAP directory initialization (389 Directory Server)
- Kerberos KDC and associated services configuration
- DNS server setup with automatic forwarders
- PKI certificate generation
- Apache configuration for web interface
- Service registration and Kerberos principals creation
The module monitors this process with a 900-second (15-minute) timeout. During this period, the container is active but services do not respond until initial configuration completes. Administrators can verify progress via docker logs -f freeipa.
Integration with Linux desktops
One of the fundamental capabilities validated during development is the enrollment of Linux workstations to the FreeIPA domain. Systems with Synex Desktop (or any compatible Linux distribution) can join the domain through ipa-client-install, obtain automatic Kerberos and LDAP configuration, and allow directory user authentication.
Users created in FreeIPA can authenticate on any domain-joined workstation, automatically obtain their home directory, and access network resources using their centralized credentials. This functionality positions Synex (both Desktop and Server) as an integrated platform for enterprise environments requiring centralized identity management.
Identity & Access Management category
FreeIPA inaugurates the "Identity & Access Management" category in ServerHub. This category groups directory services, authentication, and centralized access control, differentiating them from other categories such as collaboration, monitoring, or business applications.
The category design anticipates future additions of complementary solutions such as Keycloak (identity federation and OAuth/OIDC), standalone OpenLDAP (LDAP directory without Kerberos components), or RADIUS services for network authentication. Identity management is a fundamental pillar of enterprise infrastructure and deserves its own category in the ServerHub ecosystem.
synex-control: firewall module correction
synex-control is updated to version 1.2.1 with a behavior correction in the firewall management module.
The firewall module modified its behavior when enabling the firewall for the first time: the previous version automatically opened detected ports in active services when the user enabled the firewall. The current version removes this automatic opening, requiring the administrator to manually open necessary ports.
Active port detection remains available as a reference for the administrator, but does not result in automatically applied firewall rules. This change provides explicit control over which ports are exposed, avoiding inadvertent opening of services that the administrator might not want accessible from the network.
System updates
This version includes all cumulative package updates available in Debian Trixie repositories up to the build date. Critical security patches for server environments are incorporated, along with the optimized kernel for the amd64 architecture.
synex-installer remains in its current version with complete support for ZFS, BTRFS, ext4, and XFS.
Availability
Synex Server 13 R4 is available for immediate download. As always, we recommend verifying checksums of downloaded images before creating the installation media.
Users of Synex Server 13 R3 can update through the standard package manager. The FreeIPA module is available for installation through synex-serverhub-modules-freeipa, and synex-control automatically updates to version 1.2.1.
The incorporation of FreeIPA represents a qualitative leap in Synex Server's capabilities. Centralized identity management is not an auxiliary feature: it is fundamental infrastructure that enables real scaling of enterprise environments. A server that provides Kerberos authentication, LDAP directory, integrated DNS, and PKI in automated deployment positions Synex as a serious alternative for organizations requiring granular access control and centralized auditing.
Download Synex Server 13 R4 from here.